TRUSTED BY















OUR SOLUTIONS
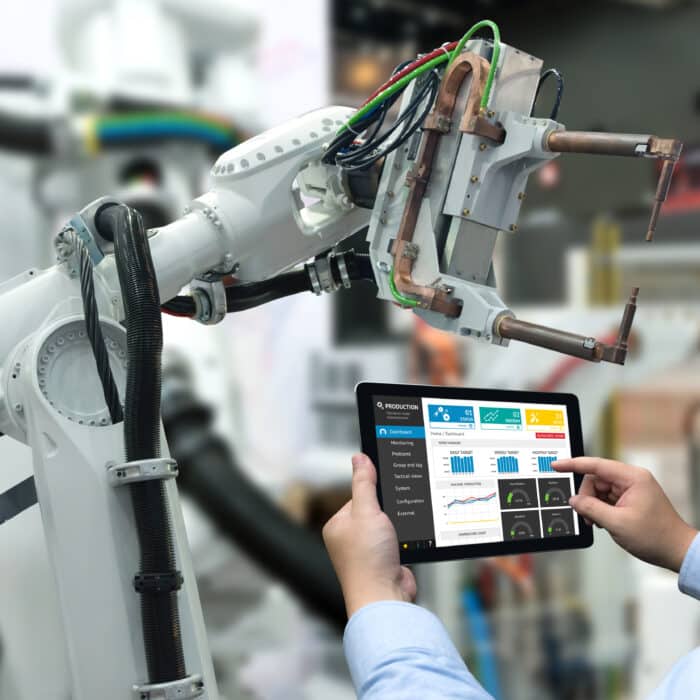
Powerful IoT Solutions
With Very, your IoT development project moves from POC to production in record time. Our tightly integrated, multidisciplinary teams harness the power of your people, products, and data to hone your vision and bring powerful IoT solutions to life.
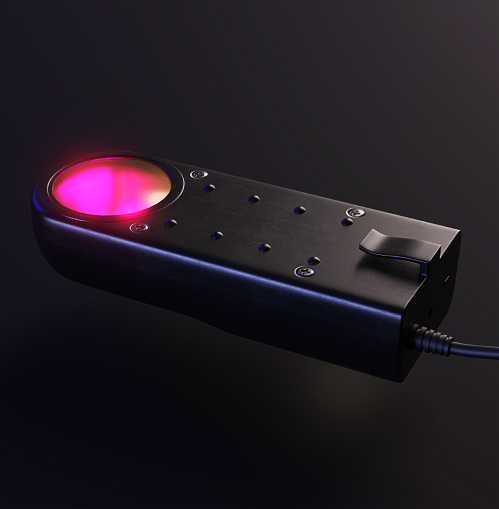
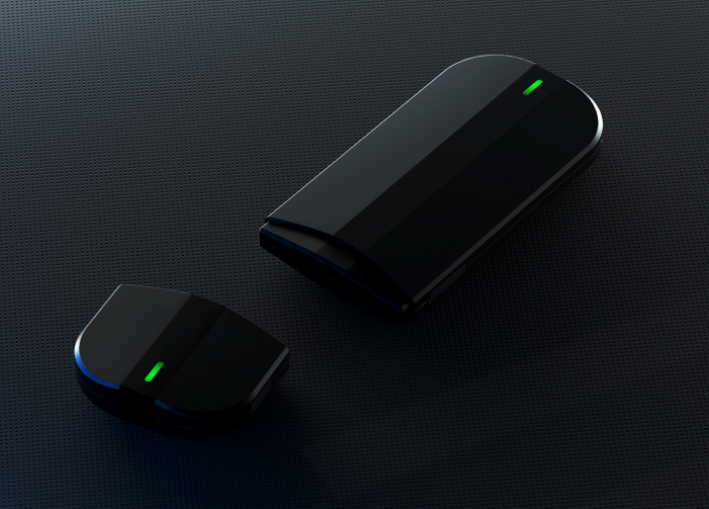
IoT Product and Interface Design
Discover, validate, and deliver seamless experiences with holistic, human-centered IoT design. We’ll ensure a seamless user experience that delivers value from day one.
Data Solutions and Machine Learning
Deploy full end-to-end data pipelines to visualize and extract actionable insights from your data. Leverage the latest machine learning and statistical methods to unlock hidden intelligence, accelerate your business and build competitive advantages.
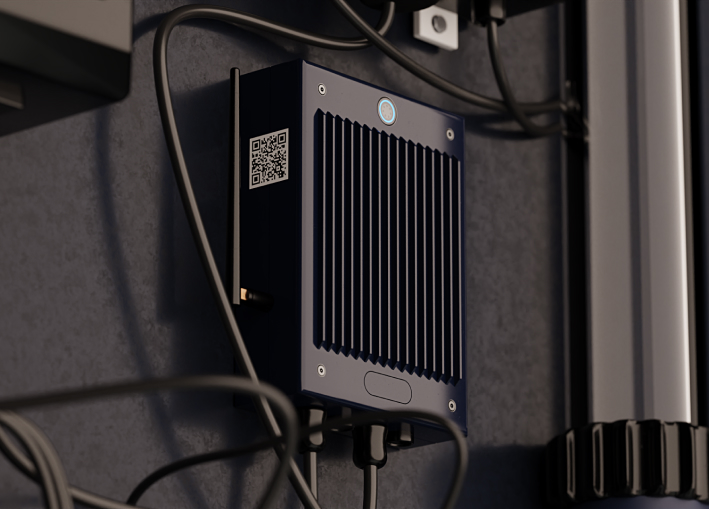
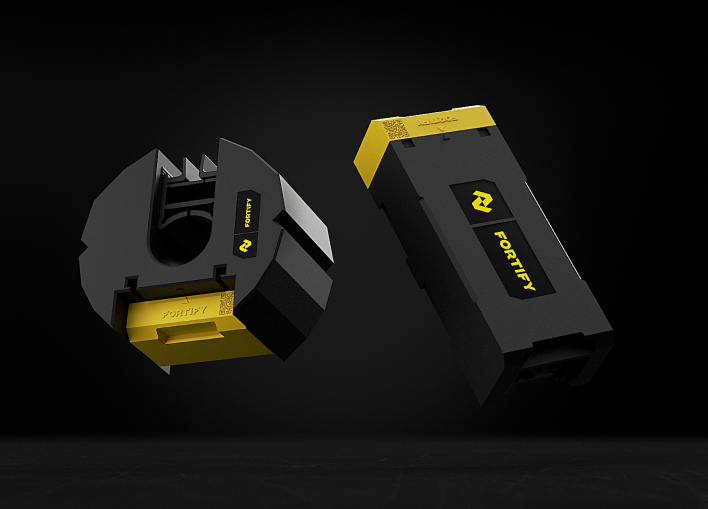
IoT Hardware and Firmware
Bring your product to market quickly with custom, rapid hardware prototyping, built with leading-edge and fully compliant electrical engineering practices.
IoT Software and Digital Infrastructure
Respond nimbly to market and product evolution with flexible software development for platforms, connected systems, web, applications, and embedded devices.
Drive Transformation With Connected Products
With over a decade of building smart and connected products for customers, Very helps enterprises push the boundaries of their current business models with elevated, strategic and human-centric solutions. We'll help you:
- Anticipate and stay ahead of your competition
- Unlock new revenue streams or a new line of business as you expand your target market reach and serve new clients or markets
- Ensure on-time delivery by reducing risk and increasing velocity
Been There, Built That
HOW WE WORK
Why Choose Very
We partner with clients to create innovative, connective products while fostering trust throughout the process. From conception through to production, our team of expert problem solvers tenaciously get to the root of your most complex challenges.

Holistic User-Centric Approach
As an end-to-end IoT development company, our unique approach to holistic engineering services focuses on the user, not the technical outcome. This approach fosters trust, proves the IoT use case, and prepares you to scale. Our approach involves:
- Gathering feedback quickly and prioritizing the building of the most essential features
- Promoting collaboration between teams to get products to market faster
- Implementing an agile methodology, allowing for continuous refinement and a quicker response to evolving project needs
Innovative IoT Solutions Built to Scale
From building smart products to end-to-end connected ecosystems, each solution is designed to help you deliver more value. Our process includes:
- Leaving room for your project to adapt as you learn more about customer needs
- Integration of hardware, software, data and design to ensure a seamless user experience
- Testing early and often to drive toward quick wins

Proven Results That Drive Your Business Forward
With over 425 projects completed, we worked with powerhouse clients, from Fortune 100 enterprises to cutting-edge, VC-backed companies, to move smart device projects from POC to production with speed and agility. We add value by:
- Providing a solution that can scale from day one to your potential deployment scenarios
- Follow industry best practices to ensure the best possible outcomes
- Ensuring a future-proof solution that remains secure, adaptable and functional as technologies advance
SUCCESS STORIES
Our Client Success Stories
Discover the impactful and innovative IoT solutions we’ve provided for our clients across various industries.